MCP Catalog
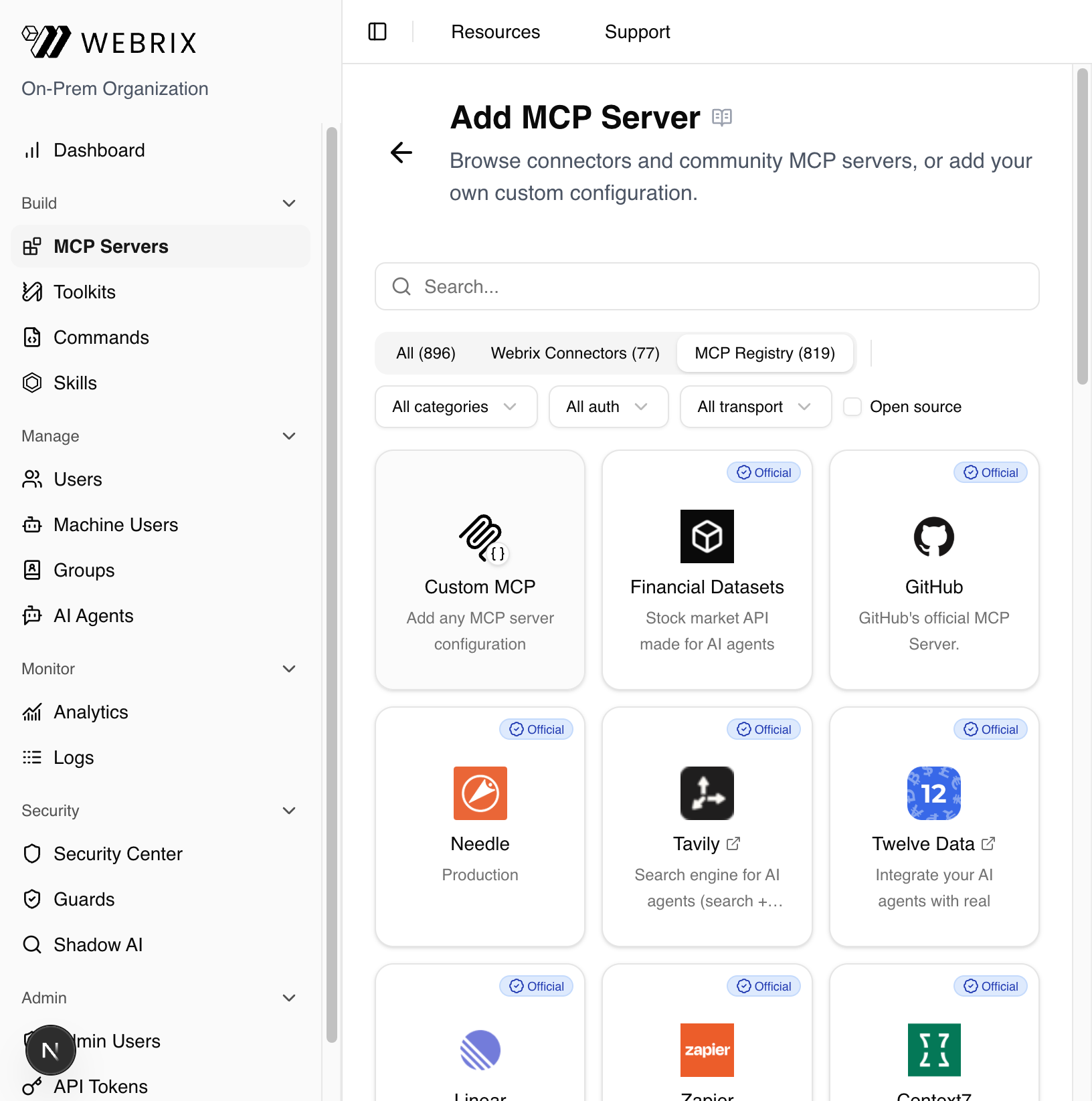
Browse and add MCP servers from the built-in catalog — includes both Webrix-managed connectors and 800+ servers from the public MCP Registry.
When to use this
- You want the fastest way to connect common tools (Slack, Gmail, GitHub, etc.)
- Your org prefers pre-vetted connectors maintained by Webrix or official publishers
- You want to browse the public MCP Registry for community and third-party servers
Steps
1. Go to MCP Servers and click "+ Add MCP Server"
In the sidebar, navigate to MCP Servers under the Build section, then click the + Add MCP Server button in the top right.
2. Browse the catalog
The Add MCP Server page opens. Use the tabs to filter what you see:
- All – shows everything (Webrix Connectors + MCP Registry)
- Webrix Connectors – pre-built, fully managed integrations by Webrix (e.g. Slack, Gmail, Jira)
- MCP Registry – 800+ community and official MCP servers from the public registry
You can also filter by category, auth type, transport, or toggle Open source only.
3. Click "+ Use" on the server you want
Hover over any card (other than Custom MCP) and click the Use button. A configuration dialog opens showing:
- The connector's name, description, and auth method(s)
- Pre-filled Name, Slug, and Type fields
- The MCP JSON configuration (pre-filled, editable)
- Links to the connector's official site and source repo (where available)
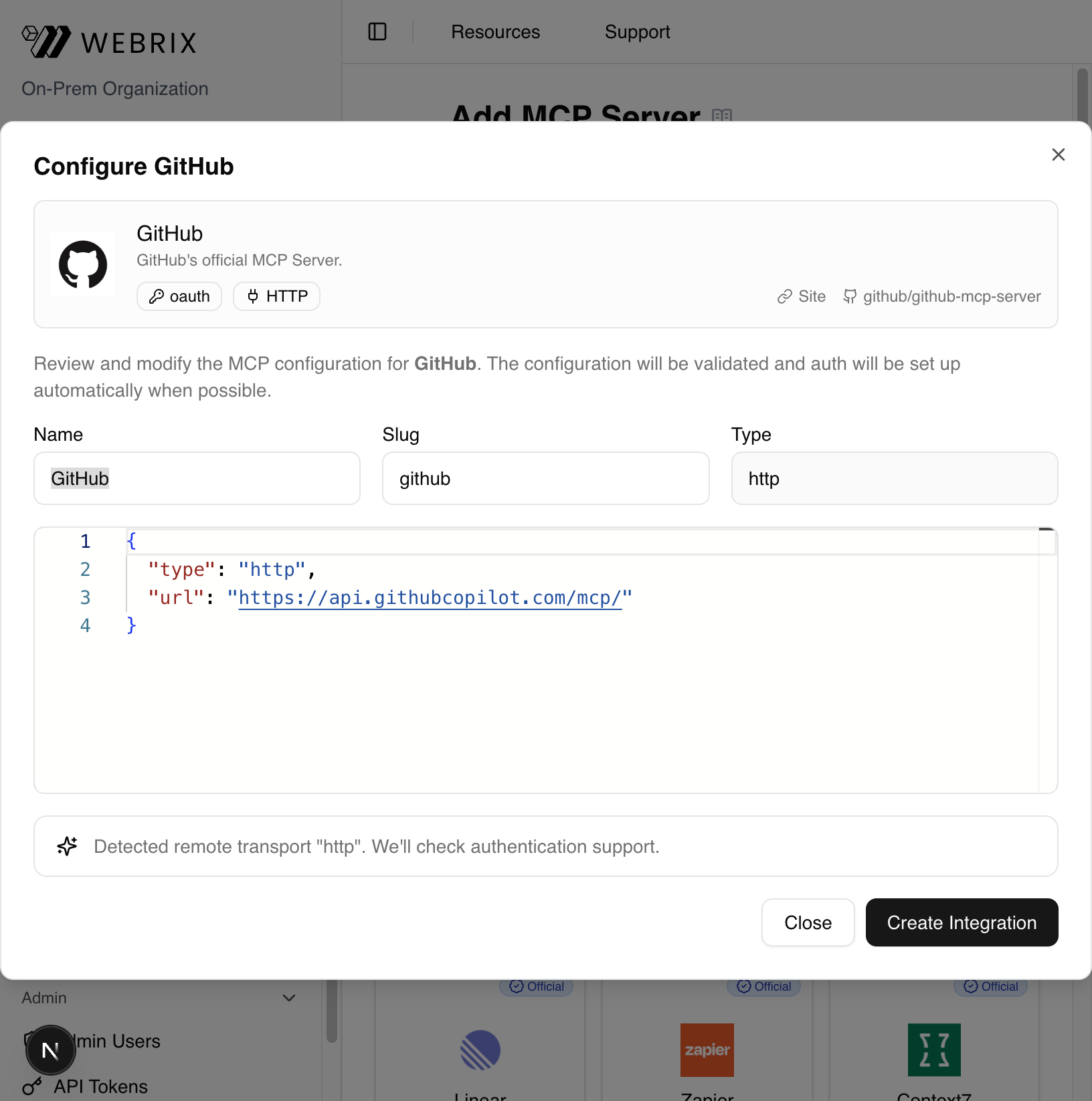
4. Review and click "Create Integration"
Review the configuration (you can edit the JSON if needed), then click Create Integration. Webrix will:
- Create a draft integration
- Apply the configuration
- Check and set up authentication automatically (OAuth, API key, etc.)
The integration appears in your MCP Servers list and is immediately available to your AI assistants.
Tips
- Webrix Connectors include built-in auth flows — no manual token management needed.
- MCP Registry servers are community-maintained; review the source repo before using in production.
- Permissions follow your org's RBAC. Admins can restrict who can use or see each connector.
- All activity is captured in audit logs for full visibility.